Technology is constantly evolving. To keep pace, the field of forensic technology – the use of technological tools and processes to aid in matters of criminal investigation – must adapt, as well. Whether you are an established forensic science technician or a student preparing for a career in any area of forensics and criminal investigation, you will need to continue learning new technologies throughout your career to stay up to date with the many types of investigative tools at your disposal. Among the most ground-breaking technological tools currently being used to help solve crimes – technologies that you must be familiar with for the foreseeable future of your work – are innovations like rapid DNA tests, forensic fingerprint analysis systems, forensic examination of data stored in the cloud, social media forensics and vehicle forensics.
Rapid DNA Tests
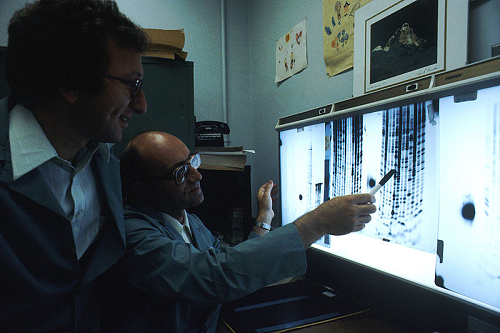
IMAGE SOURCE: Wikimedia Commons, Public Domain
Law enforcement officers can use DNA to help identify suspects – and in some situations, victims – in criminal cases. Since DNA is unique to each individual, this type of evidence is particularly compelling in a criminal investigation. The only problem is that traditional DNA tests take a long time to run – in some instances, as long as eight months. If the law enforcement department does not have sufficient evidence to keep the suspect in custody while waiting for DNA test results, a violent offender could be back out on the streets, threatening the public – or plotting their disappearance to avoid arrest.
This is where rapid DNA technology comes into play. According to the International Biometrics + Identity Association (IBIA), rapid DNA processing can be completed from 75 minutes to 90 minutes. Since law enforcement officers may have as little as two hours to charge a suspect with a crime before he or she must be released, being able to complete DNA testing in this short timeframe is a gamechanger. Instead of having to release the suspect and then try to track him or her down again later – and potentially giving the suspect time to commit more crimes or flee in the meantime – criminal investigators can use this technology to close cases faster.
Rapid DNA tests can also help victims. In a case suspected of human trafficking, rapid DNA tests can rule out a bogus claim of a family relationship. When disasters result in mass casualties, the test can more quickly bring closure to families waiting for answers.
Forensic Fingerprint Analysis
Criminal investigators have long used fingerprints to help them identify criminals and link suspects to crime scenes. Unfortunately, traditional fingerprint examination isn’t typically as accurate as DNA evidence. In the worst-case scenarios, innocent people are wrongly convicted based on traditional fingerprint evidence and dangerous criminals walk free.
An Automated Fingerprint Identification System (AFIS) helps solve this problem. These systems search through law enforcement databases of fingerprint records to identify possible matches. A highly trained fingerprint examiner reviews this list of potential masses to narrow down a list of suspects, helping investigators rule out innocent suspects and begin to focus in on the guilty party.
AFIS technology allows for better accuracy, but it still isn’t perfect. Most fingerprints recovered at a crime scene are only partial prints that must be reconstructed to be matched, which allows room for errors in traditional analysis and using AFIS technology.
Cloud Forensics
Cloud computing is so commonplace nowadays that you may think nothing of storing your data “in the cloud.” Backing up data in cloud networks allows users to save space on their personal computers and devices. Unfortunately, criminals have also found these services to be an easy way to store information without keeping it on their personal device – not to innocently preserve storage space, but to try to keep incriminating information hidden. As a result, law enforcement officers can seize the device of a perpetrator and spend hours analyzing it to no avail, because the evidence has all been moved into the network. One way cyber forensic investigators discover evidence that has been tucked away in a cloud network is by serving a warrant to the network service provider directly.
When a warrant requires the service provider to deliver the evidence directly to law enforcement, criminal investigators are able to bypass the time-consuming process of having to physically search for incriminating files and data in many different locations.
Social Media Forensics
If you think social media specialist is strictly a marketing job, you may be surprised. Most of us now have at least one social media profile, if not multiple accounts across different platforms – and many criminals don’t shy away from using these technologies, as well. Posting day-to-day activities and tagging your whereabouts is harmless fun for most of us.
When a social media user publishes something that just happens to be illegal, law enforcement can use this data against him or her in a criminal investigation and prosecution. Social media forensics refers to the collection and examination of potential criminal evidence available through social media sites.
When social media posts about illegal acts are anonymous, investigators must go through the usual channels of getting a subpoena to uncover the details. Criminals sometimes make it easy for law enforcement to track them by uploading photos or tagging their locations.
Vehicle Forensics
Cloud storage and social media aren’t the only technological changes that have made information about individuals easy to access. Many vehicles now contain an electronic system that stores data that, in some cases, can be used to help solve crimes. Modern cars have about 70 computer systems that store types of data ranging from call logs and contact lists to recent destinations and locations, the Armed Forces Communications and Electronics Association (AFCEA) reported. This data can be extremely important for criminal investigations, the AFCEA reported. A forensic examination of a vehicle’s computers can place suspects at the scene of a crime or even reveal possible coconspirators.
An examination of a vehicle’s computer may reveal a list of mobile devices that have been connected to the vehicle through Bluetooth. In some criminal investigations, officers have used this Bluetooth connection to access data about phones that might be locked otherwise.
Additional Resources
What Are the Career Options for Forensic Technology?
Which Science Would Be the Best to Study in Order to Become a CSI?
What Kind of Computer Degree Is Most Helpful in Getting a Job in Cyber Security?